🔍 Search
📥 Subscribe
Distributed Denial of Service (DDoS) Attack
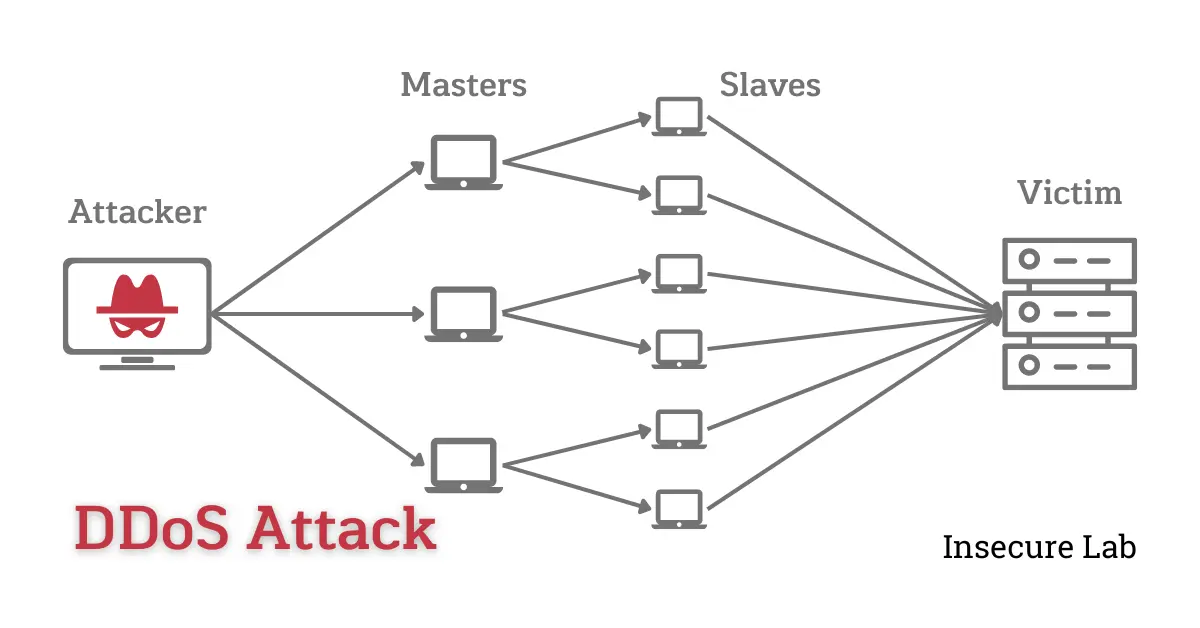
Table of Contents:
What is DDoS Attack ?
A Distributed Denial of Service (DDoS) attack is a malicious act in which a targeted system, network, or website is overwhelmed with a flood of incoming traffic from multiple sources.
Unlike a regular Denial of Service (DoS) attack, which involves a single source flooding the target, a DDoS attack utilizes a network of compromised computers or devices known as a botnet. These compromised machines, often controlled by the attacker remotely, are used to generate and direct a massive volume of traffic towards the target simultaneously.
How DDoS Attack Works ?
DDoS attacks work by overwhelming the targeted system or network with a large volume of traffic, rendering it unable to handle legitimate requests. Here is a general overview of how a DDoS attack works:
-
Botnet Creation:
The attacker typically assembles a botnet, which is a network of compromised computers or devices under their control. These compromised machines are often infected with malware or controlled through other means, allowing the attacker to command them remotely. -
Reconnaissance:
The attacker identifies the target they wish to disrupt or damage. This could be a specific website, an online service, or an entire network infrastructure. -
Command and Control:
The attacker communicates with the compromised machines in the botnet, instructing them to launch the DDoS attack. The communication is usually done through a command and control (C&C) infrastructure that coordinates the activities of the botnet. -
Attack Initiation:
The attacker directs the botnet to flood the target with a massive volume of traffic. The traffic can be generated using various techniques, including sending excessive data packets, initiating numerous connection requests, or overwhelming specific services or protocols. -
Traffic Overload:
The target system or network becomes inundated with the high volume of incoming traffic. This flood of traffic consumes the target's resources, such as bandwidth, processing power, or memory, exceeding its capacity to handle legitimate user requests. -
Service Disruption:
As the target's resources are exhausted, it becomes unable to respond to legitimate traffic effectively. This results in a denial of service to genuine users trying to access the targeted system or network. -
Attack Persistence:
DDoS attacks can continue for a prolonged period, often until the attacker decides to stop or until countermeasures are implemented to mitigate the attack. Attackers may employ tactics to evade detection or adapt their attack strategy during the course of the attack to bypass defenses.
Types of DDoS Attack:
There are several types of DDoS attacks, each targeting different aspects of a system or network. Here are some common types of DDoS attacks:
1. Volumetric Attacks
These attacks aim to saturate the target's network bandwidth by flooding it with an overwhelming volume of traffic. The goal is to exhaust the target's resources, making it unable to handle legitimate requests. Examples include UDP floods, ICMP floods, and DNS amplification attacks.
2. TCP/IP Attacks
These attacks exploit vulnerabilities in the TCP/IP protocols to disrupt network connectivity. For instance, SYN floods overwhelm the target's capacity to establish and maintain TCP connections by flooding it with a flood of SYN requests, depleting the available resources.
3. Application Layer Attacks
Application layer attacks target specific services or applications running on the target. They exploit weaknesses in the application layer, such as the HTTP protocol, by overwhelming the server with requests or exploiting resource limitations. Examples include HTTP floods, Slowloris attacks, and application-specific attacks.
Prevention:
Preventing DDoS attacks entirely is challenging, as attackers are continually evolving their tactics. However, you can take proactive measures to reduce the risk and minimize the impact of DDoS attacks.
Here are some preventive measures to consider:
-
Scalable Network Infrastructure:
Build a scalable network infrastructure that can handle increased traffic during an attack. This involves using Content Delivery Network (CDN) for distributing your resources across multiple servers or data centers, utilizing load balancing mechanisms, and implementing redundancy in critical components. Scaling your infrastructure helps to absorb and distribute the impact of a DDoS attack, minimizing its disruption. -
Traffic Filtering and Access Control:
Utilize traffic filtering mechanisms, such as Access Control Lists (ACLs), to restrict traffic to your network. Implement whitelisting or blacklisting rules based on trusted IP addresses or ranges. This helps block traffic from suspicious or known malicious sources and reduces the attack surface. -
Rate Limiting and Connection Throttling:
Implement rate limiting and connection throttling mechanisms to control the number of requests or connections allowed from a single IP address or source. By limiting the rate at which connections or requests are accepted, you can mitigate the impact of an attack by slowing down the attacker's ability to flood your resources. -
Bandwidth Management and Traffic Shaping:
Employ bandwidth management and traffic shaping techniques to allocate network resources effectively. By prioritizing traffic based on importance and employing Quality of Service (QoS) policies, you can ensure that critical applications and services receive sufficient bandwidth during a DDoS attack, reducing the impact on legitimate users. -
Traffic Monitoring and Anomaly Detection:
Implement comprehensive network monitoring and traffic analysis tools. These systems can help identify unusual traffic patterns and behavior, enabling you to detect and respond to potential DDoS attacks in real time. Anomaly detection algorithms and intrusion detection systems can assist in early warning and alerting. -
Firewalls and Intrusion Prevention Systems (IPS):
Deploy robust firewalls and IPS devices at the network perimeter to filter and block malicious traffic. These devices can identify and block known attack signatures, filter out illegitimate traffic, and provide an additional layer of defense against DDoS attacks. -
Incident Response Planning:
Developing a robust incident response plan is crucial for effectively mitigating the impact of DDoS attacks. This plan should outline roles, responsibilities, and steps to be taken during an attack, allowing for a swift and coordinated response.
Summary:
DDoS attacks can have severe consequences for individuals, organizations, and even entire sectors of the economy. Downtime resulting from a successful DDoS attack can lead to significant financial losses for businesses. Unavailable services, reduced productivity, and potential reputational damage can result in direct revenue losses and increased recovery costs. Therefore, implementing robust security measures and employing DDoS mitigation techniques is crucial to protecting against these disruptive attacks.
